CMMC Compliance Consultation
We are conducting a consultative session on CMMC controls. It is hosted by a CMMC Registered Practitioner (RP), that will conduct a detailed assessment of your current technology, processes, and documentation of evidence, against the controls required by CMMC. The aim is to enable you to identify the objective evidence required by auditors and recommend ways to document it, based on your current and planned cybersecurity practices.
Our CMMC expert will help you understand:
- The different types of evidence auditors require
- How to find out more about addressing a confusing control
- Best practices for documenting policy appropriately
Schedule Your Free Consultation
By setting up your free CMMC consultation you'll also be given a FREE CMMC Checklist to get you going in the right direction!
The Department of Defense has made it very clear they want their contractors to prepare now for Cybersecurity Maturity Model Certification. How organizations prepare and achieve DOD cybersecurity maturity model certification can be a difficult, intimidating, complex process for a lot of people.
But it's not for us.
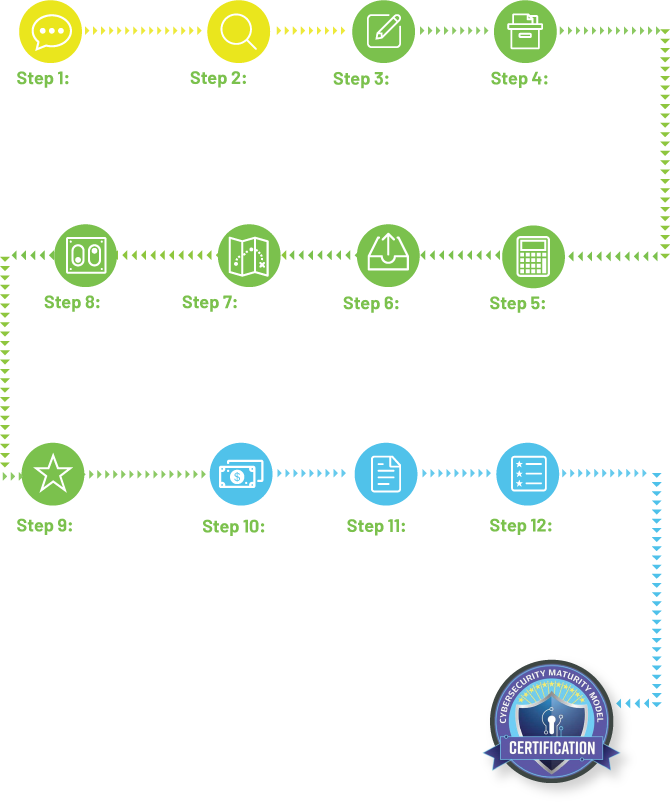
The Winsor Consulting process for CMMC compliance and certification will include the following steps:
- Determine your maturity level requirement
- Perform a gap analysis
- Remediate identified gaps
- Engage with an assessor
- Apply for CMMC certification

Registered Practitioners
In-Depth Gap Analysis
Remediate Identified Gaps
With Winsor Consulting, You're In Good Hands.
Talk with a CMMC Registered Practitioner (RP) today to start your path to compliance and get a sense of what other small to mid-sized companies are doing to increase their SPRS Risk Score and prepare for their CMMC audit.
